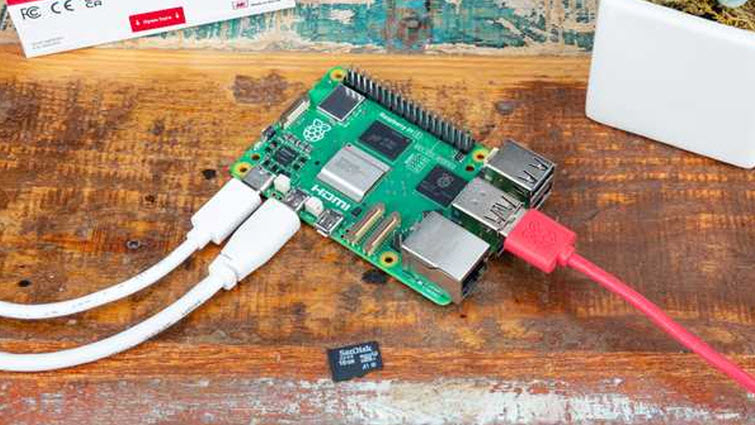
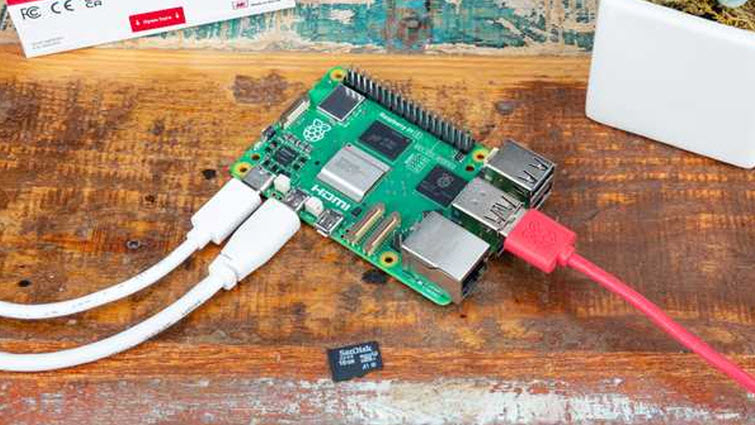
Top 5 hacking tools that can fit in your pocket
Hey there, fellow security enthusiasts! Ever wondered how blue teams defend while red teams attack? It’s all about working together towards a common goal – identifying and addressing gaps in […]
Hey there, fellow security enthusiasts! Ever wondered how blue teams defend while red teams attack? It’s all about working together towards a common goal – identifying and addressing gaps in […]

Benefits of Workflow Automation in Service Delivery Workflow automation plays a crucial role in improving service delivery by streamlining processes and increasing efficiency. It eliminates the need for manual handling […]

Email has become a vital tool for communication in today’s interconnected digital landscape. However, with the convenience of email also comes security risks. Unprotected email accounts are vulnerable to cyber […]

Memory forensics plays a crucial role in incident response and threat analysis in the ever-evolving cybersecurity landscape. Unlike traditional methods that focus on hard drive analysis, memory forensics delves into […]

Endpoint Threat Detection and Response Solutions Explained Are you wondering what Threat Detection and Response Solutions entail? If your device is connected to the internet or part of a closed […]
Exploring the array of SOC automation tools and trends can be daunting, especially with the rapid emergence of new artificial intelligence technologies in 2024. Security Operations Centers (SOCs) must adapt […]