
The psychology behind phishing
When it comes to cybersecurity, the focus is often on technical defenses against attacks. However, understanding the psychological aspects of phishing is just as crucial in comprehending the exploitation of […]

When it comes to cybersecurity, the focus is often on technical defenses against attacks. However, understanding the psychological aspects of phishing is just as crucial in comprehending the exploitation of […]

In the year 2025, phishing attacks have evolved to become more sophisticated than ever before, utilizing advanced technology to trick both individuals and organizations. Here are the latest trends to […]

Scammers are now using generative AI to craft phishing emails that can bypass language barriers, respond in real-time, and automate large-scale personalized campaigns, making it easier to impersonate domains and […]
26 Hey there, have you heard about the latest phishing attack using Google Calendar to slip past security measures? It’s a pretty sneaky tactic that cyber attackers are using to […]

Hey there! I’m sure you’ve heard of phishing, the sneaky email attack that tricks people into sharing sensitive information. It can lead to website downtime, data loss, revenue drops, and […]

Hey there! Let’s chat about phishing scams because, let’s face it, they’ve become pretty sneaky. What used to be obvious spam now looks like a message from a friend, a […]

44 Hey there, have you heard about the latest phishing campaign that’s making the rounds? It’s pretty sneaky! So, imagine this – you visit a website, and suddenly you’re asked […]

Hey there, are you part of a business that’s using Microsoft 365 for communication and collaboration? If so, you’re probably aware of how crucial email security has become in today’s […]
October 2023 Update: Intezer analyzes all URLs that we collect as evidence for automated alert triage, which now includes detecting and extracting QR codes for phishing email investigations. At Intezer, […]
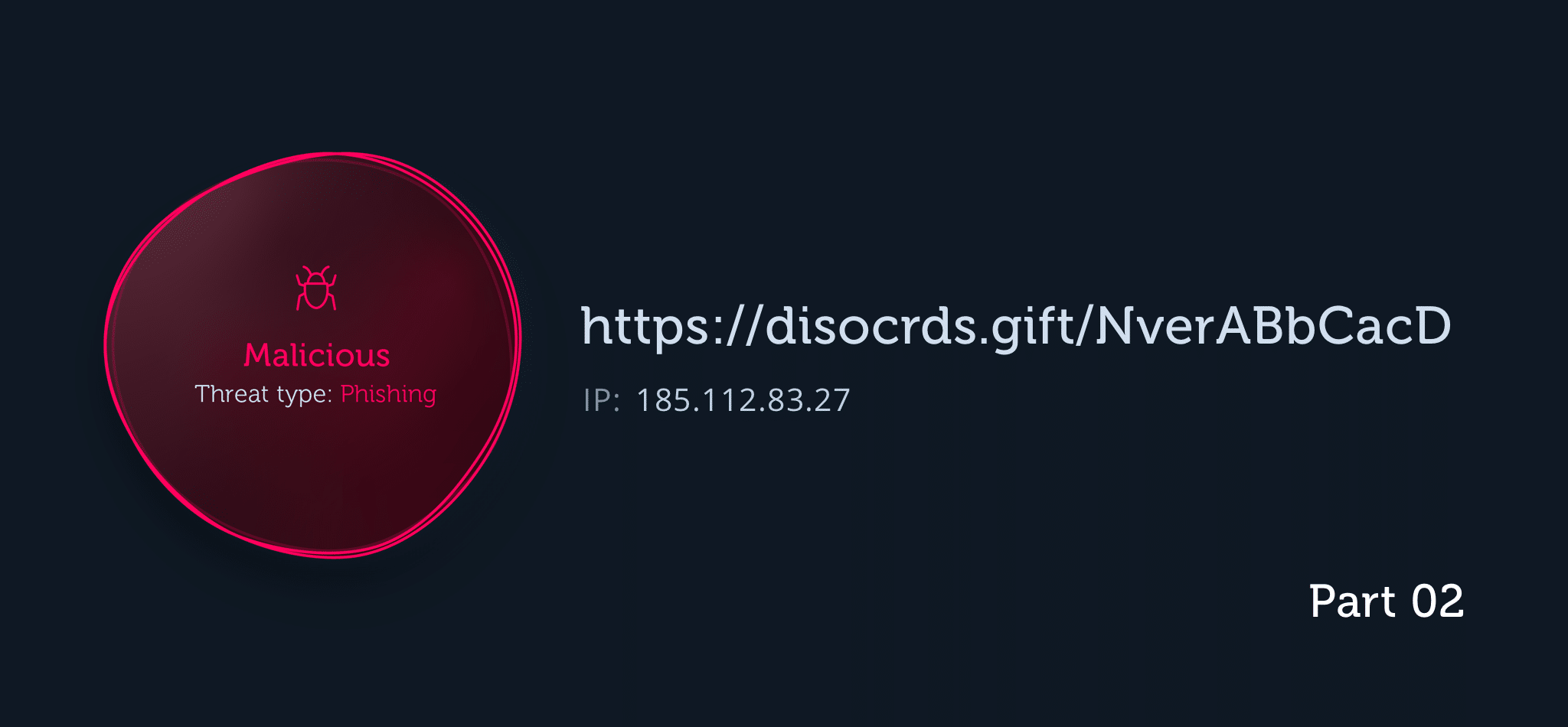
Analyzing suspicious URLs on an individual basis can be tricky, but when you’re facing a large volume of potentially malicious URLs then other approaches that leverage automation (like machine learning) […]