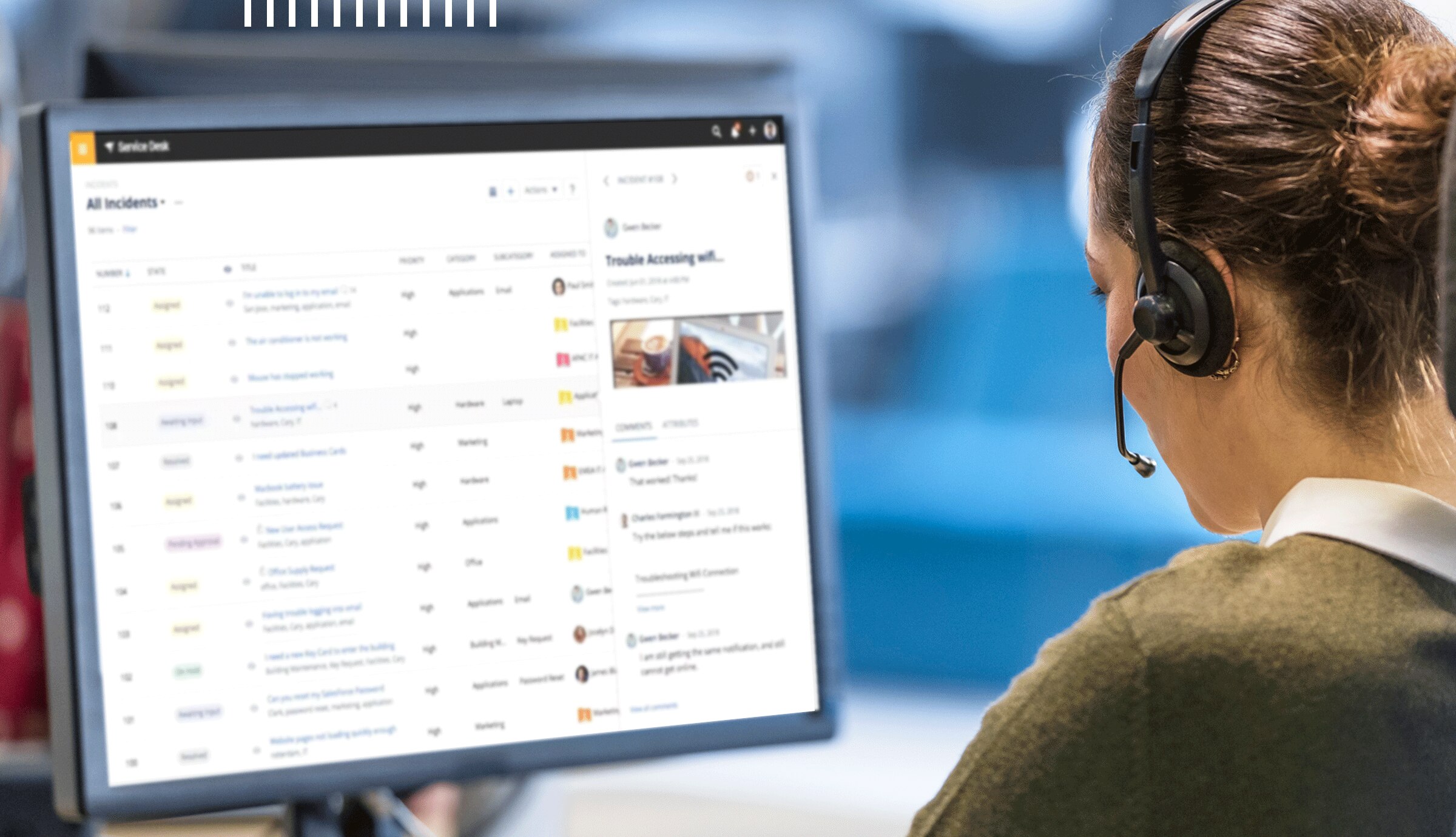
4 Strategies for Optimizing the ITSM Portal in Your Organization
Welcome to our discussion on the importance of an effective IT Service Management (ITSM) portal for maintaining operational excellence. Today, we are joined by Senior IT Manager Noel Barbee, who […]